Convergence – My last post created some typical requests from regular readers about simplifying the post. As most of the reader mentioned it was too technical and difficult to understand, “PCRF the Liberator for Mobile Data Charging”. Here I am again attempting to make every effort to address & taking care of the feedbacks. Re-writing this as an extended version of the last one with much more simple language and example from real life.
Data Charging – The Amount Charged to a Mobile Phone Account
It’s a learning for me as well on how to share what I know. How to Interface, with subscribers of different segments is not like a drag-and-drop GUI (Even though this will be difficult for some). Customers are 1st priority hence should be dealt like P1 service quality.
At present when MNO’s across the globe are hard-pressed for their revenues & pushed to increase service quality and increase new service portfolios. At the same time, MNO’s are choosing disruptive technology and approach to serve digital services to consumers. Focus on Mobile data users who are on rising in multiple folds.

Data charging is the amount charged to a mobile phone account for data access, which in most cases refers to Internet-based data. Data charging usually follows either of two models: pay-as-you-use (less than 1% contribution from my own experience) or Pre-set (bundles, etc., which is close to 99%).
With the rise of smartphones and tablet PCs and the subsequent demand for web-based services, carriers have been trying to compete with each other with more attractive data charging schemes. With the pay-as-you-use data charging scheme, subscribers are charged based on either the total number of hours used or the total amount of data downloaded.
Online Charging System (OCS) or any Typical IN System
MNOs are making great progress with great speed to ensure and answer themselves on how they can create a digital experience that their customers are shouting about or asking for. MNOs are working hard to ensure service control points remain under their control, but the presentation and experience of self-control to consumers To provide services, including call access and signaling control, service logic management, Basic data operation, and processing, are a few examples here.
The general front-end processor or handset is mainly used to exchange data between other communication entities, for example, the message transfer between the handset and the pre-delivery service agent or business rules in the provider’s system. Any Online Charging System (OCS) or any typical IN system, which is a uniform charging platform that helps MNOs charge voice, data, and multimedia services on fixed, mobile, and data networks,
The charging and billing system helps MNOs conform to the complicated operation environment, new services, different cooperators, and detailed customer types.
The charging and billing system can run on the Global System of Mobile Telephone (GSM) network, the Code Division Multiple Access (CDMA) network, the Time Division Multiple Access (TDMA) network, the Session Initiation Protocol (SIP) network, and the Next Generation Network (NGN). In addition, the system can precisely control the credit limit for subscribers to the maximum. In this way, the risk of arrears can be reduced, and the revenue loss of carriers can be reduced accordingly for most of the services.
Sadly, data services lack the need of today’s time, so here comes PCRF to complement and fix all the potholes for mobile data charging. Policy and Charging Rules function, i.e., pcrf, that supports service data flow detection, policy enforcement, and flow-based charging. PCRF is part of the evolved packet core (EPC) and a kind of saviour for the provider so that it can satisfy more policy control use cases faster on policy enforcement infrastructure.
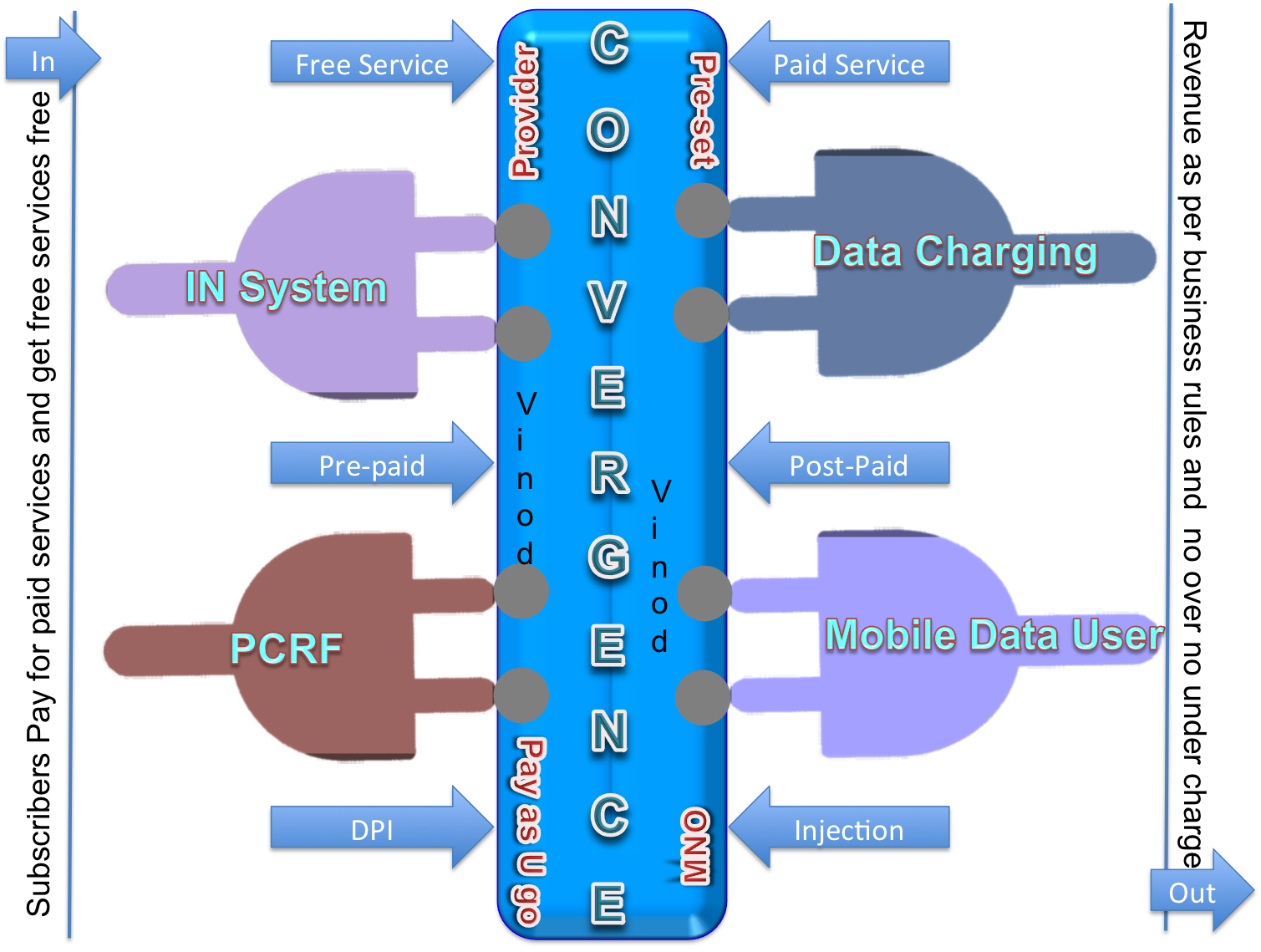
Convergence – Intelligent System, Mobile Data Charging and PCRF
The convergence of intelligent systems, Mobile Data charging, and PCRF was the biggest breakthrough and reason for the big smile on providers’ faces. The IN (Charging and Billing System) system provides functions such as Product management, Resource management, Rating and billing, Credit control, Recharge centres, Call control, and Customer care. The IN system has good expandability and convergence.
Through convergence with the external charging system, the IN system can provide a uniform charging platform, a uniform service management platform, and a uniform customer care platform for prepaid and postpaid subscribers. The IN system provides a uniform charging platform and flexible charging policies for multiple telecommunication services, such as voice, short message, and data services used by prepaid and postpaid subscribers. The IN system supports telecommunication services such as voice service, short message service, data service, ring-back tone service, and recharging services.
The web browsing service provides online services through web protocols. The mobile subscriber accesses an application server through an internet gateway to obtain information. Subscribers browse web pages, news, music, videos, and pictures through a mobile terminal. The IN system supports the charging and rental of a subscriber based on the contents, traffic, and duration of the web browsing service in conjunction with business rules defined under PCRF.
The IN system provides accurate and flexible charging methods, such as prepaid charging, postpaid charging, and credit-based postpaid charging. Issues that critically assess the vulnerability of 3G and 4G charging systems The discovery of loopholes in policy practice and weaknesses in charging system architecture was fixed with PCRF. As a result, revenues moved in the correct direction. Tight control of service quality is critical for operators to establish new business models and monetize services.
Security of Charging and Billing Systems
Attacks or fraudulent injections on charging and billing systems, i.e., the toll-free data access attack, allows attackers to access any data service from the mobile phone for any period of time free of charge. It exploits policy loopholes when the operator allows for certain free services. In a stealth spam attack, attackers will inject an arbitrarily large volume of spam data into the victim’s device, even after the target device has terminated its data service, thus making the victim fully unaware of such spam.
This attack exploits the architecture weakness of not using feedback from the user when making charging decisions, as well as features of Internet instant messaging applications (e.g., Skype, What’s App, etc.). Prototypes showed that both attacks were feasible and simple enough to launch over the operational 3G networks. Some experiments on two 3G networks from two US carriers showed that the undercharge or overcharge traffic volume can go unbounded.
Pay-as-you-go and pre-set are two different models that serve two different segments of customers. A pre-set model (data bundling) is based on the size of the Web page or downloaded data, in kilobytes or megabytes. Thus, pages with only text are less expensive than pages with images. With the pre-set charging scheme, subscribers are given a maximum download limit (data volume or quantity of data) per month. For example, a data plan features 10 GB of data access per month. Users can access the Internet as often as they desire until they hit the 10 GB limit.
However, there are no extra charges for exceeding the limit. But the user’s download speed is curtailed until the next billing cycle (for post-paid users) or the disconnection of data services as soon as the user runs out of his limit (for pre-paid users) unless the user recharges again. Pay-as-you-use is the cheaper data charging scheme for users who only occasionally go online. Users who are frequently checking and want to be on Facebook, What’s an App, Twitter, other messengers, browsing the web, watching YouTube, and so on, find this option to be extremely expensive. Data bundles are the best for this category.
Data Science and AI-based Quality Control
Quality control enables operators to employ fair-use policies that limit subscriber service abuse and maintain network performance during peak traffic times. Undisputed and uninterrupted services in best-of-breed network policy control and class should be the motive or actually are the motive, for every service provider. The policy engine empowers hundreds of communications channels that are based on fair-use policies, congestion-free management solutions, quota-based plans, and wildly innovative prepaid and postpaid subscriber services.
Before commenting on the heavy capex of billions of dollars on equipment and deployments, forward-thinking operators will carefully evaluate vendors and proactively measure the quality of service and policy management functions of their network devices. Validating mobile data service quality requires saturating the network with a high load of real-world mobile subscriber traffic and measuring key performance indicators that identify the quality of the experience. The rapid growth in mobile broadband has been a great success story, but one that has left in its wake many challenges as well as opportunities for mobile operators.
The rise and adoption of smartphones are major triggers for service providers to move in this direction. Smart devices in many markets now account for over half of new devices and the total subscriber base, and the extensive availability of applications and services, with video accounting for over half the traffic, has created a surge in the data load on the networks.
More the Traffic More the Knowledge
Accommodating the increased traffic volume can be an expensive proposition for mobile operators, and yet discouraging subscriber use limits the opportunity for revenue growth. Tomorrow’s hot app or new service requests can show up without warning, and the service provider needs to be able to move quickly to take advantage of new opportunities and respond to competitive threats. As subscribers will demand the same service on the same day. It’s very impatient, service-demanding at a lower cost, and always ready for new things on the market.
By productizing policy control and making service definition accessible, MNOs need to act when they’re required to act right now. With the service delivery engines, launching any new service should be swift and not require any waiting.
Fair and transparent charging should be the motive of any service provider at all times. Marketing communication and educating your customers on price plans and usage policies should be on the clear agenda and ready to avail information. I gave this example in my post last year.
For instance, if you move your network from 2G to 3G or from 3G to 4G and tell your customer to use the faster connection and enjoy speedy data, the next day the customer will complain that you (the service provider) stole his money and will never realize that his or her data now would not last for 30 days due to speed and may vanish in 15 days as the package bought was on the total data amount and not unlimited data under a time-bound package.
When a customer uses 1 GB of data on the 2G network, it may take 30 days (Just for argument’s sake), on 3G it might vanish in 22 days, and on 4G it might take just 10 days to be consumed, and the customer says, What!!! Where is my data? and accuses the provider of stealing his data or money. When we advertise something like Limited Possibilities, which is very Easy To Use, this marketing language needs to be explained to customers in their own easy way, as it looks very deceptively simple to use but is impressively difficult for some.
The tight interdependency between DPI, policy rules, and policy enforcement presents a strong case for integration to enable mobile operators to leverage DPI data in defining and enforcing policy while keeping complexity under control and enabling a fast time-to-market deployment.
With PCRF capabilities and MNO’s service delivery engine, this is feasible. The PCEF (Policy and Charging Enforcement Function) selects a PCC rule for each received packet by evaluating received packets against service data flow filters of PCC rules in the order of precedence of the PCC rules. When a packet matches a service data flow filter, the packet matching process for that packet is completed, and the PCC rule for that filter shall be applied.
MNOs keep talking and advertising about 3G, 4G, 5G, this G and that G, giving subscribers the feeling of OMG, but in reality, subscribers’ smartphones rock, but providers’ networks stink. Well, what has happened and is happening with tens of millions of customers around the globe is LTE Hell, but they joined the beautiful 4G LTE network. Rate capping and introducing expensive overage charges for bandwidth hoggers have become the norm.
By leveraging prepackaged building blocks and setting their own conditions and values, they can design and deploy a new service in minutes without worrying about what’s happening behind-the-scenes. “Unlimited” legacy data plans by all of the main carriers have been eliminated.
The joint implementation of DPI and Policy enables operators to optimize network resource allocation, to segment their subscriber-ship effectively, and to create value-based, personalize services. This, in turn, may lead to improved network performance and utilization, a higher perceived value for the service, lower churn, and expanded revenue opportunities. When a service provider launches a super service that gives unlimited use of the latest app or just update fair-use policy, this needs time and clear communication.

================================= About the Author ===============================
Read about Author at: About Me
Thank you all, for spending your time reading this post. Please share your feedback/comments/critics/agreements or disagreement / remark for more details about posts, subjects and relevance please read the disclaimer.
Facebook Page Twitter Blog Linkedin Pulse ==========================================================